This set of Cryptography Multiple Choice Questions & Answers (MCQs) focuses on “Block Cipher Systems”.
1. In affine block cipher systems if f(m)=Am + t, what is f(m1+m2) ?
a) f(m1) + f(m2) + t
b) f(m1) + f(m2) + 2t
c) f(m1) + t
d) f(m1) + f(m2)
View Answer
Explanation: In general f(∑(i=1 to n) m_i = ∑(i=1 to n) f(m_i) + tδ_n) where δ_n=0 if n is odd and 1 if n is even.
2. In affine block cipher systems if f(m)=Am + t, what is f(m1+m2+m3) ?
a) f(m1) + f(m2) + f(m3) + t
b) f(m1) + f(m2) + f(m3) +2t
c) f(m1) + f(m2) + f(m3)
d) 2(f(m1) + f(m2) + f(m3))
View Answer
Explanation: In general f(∑(i=1 to n) m_i =∑(i=1 to n) f(m_i ) + tδ_n) where δ_n=0 if n is odd and 1 if n is even.
3. If the block size is ‘s’, how many affine transformations are possible ?
a) 2s (2s-1)(2s-1)(2s-12)………(2s-1(s-1))
b) 2s (2s-1)(2s-2)(2s-22)………(2s-2(s-2))
c) 2ss (2s-1)(2s-2)(2s-22)………(2s-2(s-1))
d) 2s (2s-1)(2s-2)(2s-22)………(2s-2(s-3))
View Answer
Explanation: 2s (2s-1)(2s-2)(2s-22)………(2s-2(s-1)) is the maximum number of affine transformations possible for a block size ‘s’ matrix.
4. What is the number of possible 3 x 3 affine cipher transformations ?
a) 168
b) 840
c) 1024
d) 1344
View Answer
Explanation: Since ‘A’ cannot have columns of ‘0’s. so there are ‘7’ choices i.e. 001/010/011/100/101/110/111. ‘a1’ is chosen for first column of ‘A.
We have ‘6’ choices for second column, let ‘a2’ be chosen for second column.
The final column can be any 3-tuple except 0, a1, a2, a1+a2. That means any one of the remaining ‘4’ 3-tuples may be chosen for the final column.
(Total number of@ possibilities for A)}=k=7×6×4=168
(Number of affine@ block cipher transformation)}=k×t=8×168 =1344
5. Super-Encipherment using two affine transformations results in another affine transformation.
a) True
b) False
View Answer
Explanation: f(g(m))=A_1 g(m)+c_1
f(g(m))=A_1 (A_2 m+c_2)+c_1 f(g(m))=A_1 A_2 m+A_1 c_2+c_1 f(x)=A_3 m+c_3
where
A_3=A_1 A_2
c_3=A_1 c_2+c_1
This results in another affine transformation, and does not improve the security.
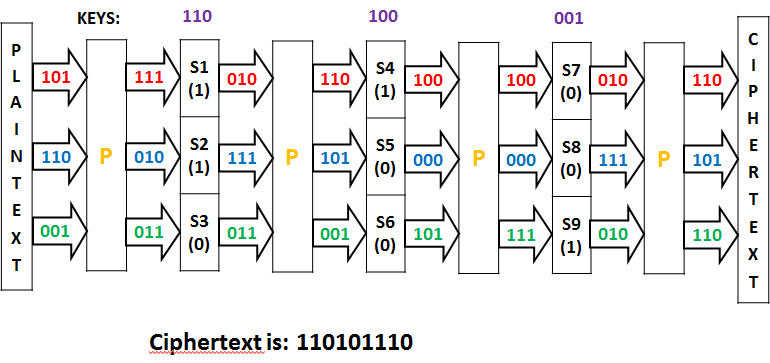
6. If the key is 110100001, the output of the SP network for the plaintext: 101110001 is
a) 110100011
b) 110101110
c) 010110111
d) 011111010
View Answer
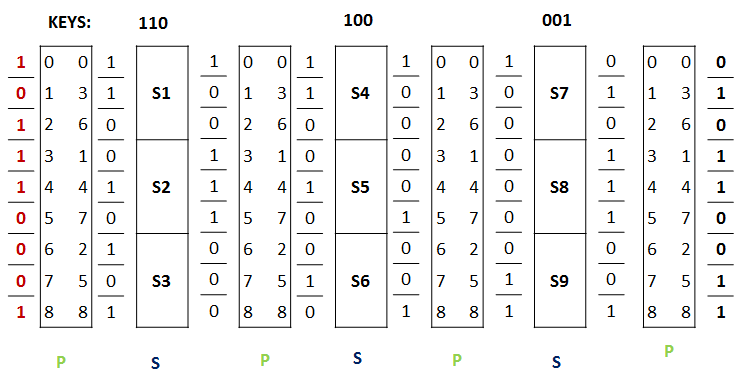
7. If the key is 110100001 where,
If ki=0, then S_i (x)=((1 1 0 | 0 1 1 | 1 0 0 ))x+((1 1 1))
and If ki=1, then S_i (x)=((0 1 1 | 1 0 1 | 1 0 0))x+((0 1 1))
then the output of the SP network for the plaintext: 101110001 is
a) 010110011
b) 111000011
c) 110110111
d) 010110110
View Answer
8. Confusion hides the relationship between the ciphertext and the plaintext.
a) True
b) False
View Answer
Explanation: Confusion hides the relationship between the ciphertext and the key.
9. The S-Box is used to provide confusion, as it is dependent on the unknown key.
a) True
b) False
View Answer
Explanation: The S-Box is used to provide confusion, as it is dependent on the unknown key.
The P-Box is fixed, and there is no confusion due to it, but it provides diffusion.
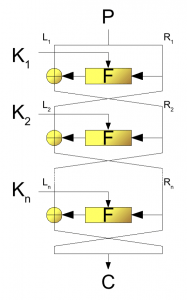
a) SP Networks
b) Feistel Cipher
c) Hash Algorithm
d) Hill Cipher
View Answer
Explanation: The figure is the Feistel Cipher Structure.
11. Which of the following slows the cryptographic algorithm –
1) Increase in Number of rounds
2) Decrease in Block size
3) Decrease in Key Size
4) Increase in Sub key Generation
a) 1 and 3
b) 2 and 3
c) 3 and 4
d) 2 and 4
View Answer
Explanation: Increase in any of the above 4 leads to slowing of the cipher algorithm i.e. more computational time will be required.
Sanfoundry Global Education & Learning Series – Cryptography and Network Security.
To practice all areas of Cryptography and Network Security, here is complete set of 1000+ Multiple Choice Questions and Answers
If you find a mistake in question / option / answer, kindly take a screenshot and email to [email protected]
- Check Cryptography and Network Security Books
- Check Computer Science Books
- Practice Cyber Security MCQ
- Practice Computer Science MCQs
- Apply for Computer Science Internship